ERP & eShop in the Cloud: The Hidden Risks — and How to Protect Your Business
If your ERP or eShop is online, it is exposed.
Today, more and more businesses operate:
- ERP systems hosted in the Cloud or on Azure
- B2B and B2C eShops
- CRM portals
- Web applications
- Public APIs for partners and integrations
24/7 availability is essential.
But that also means your infrastructure is accessible from anywhere in the world — not only by customers.
And a significant portion of internet traffic does not come from real users.
The Main Risks for eShop & Cloud ERP Environments
1. Brute Force & Credential Stuffing Attacks
Automated bots attempt thousands of login combinations against:
- ERP portals
- Admin panels
- B2B customer accounts
Even when unsuccessful, these attempts consume:
- CPU and RAM
- Database connections
- Network bandwidth
- Cloud resources
Over time, this leads to increased infrastructure costs and performance degradation.
2. Price & Data Scraping
Automated tools can:
- Download entire price lists
- Monitor promotional changes
- Collect product and commercial data
Without your knowledge.
In B2B environments, this can mean exposure of sensitive commercial information.
3. API Abuse
If your ERP or eShop exposes APIs:
- Excessive automated requests can overload services
- Resource consumption may spike unexpectedly
- Performance issues may affect legitimate users
In Azure or other cloud environments, this often translates directly into higher operating costs.
4. Web Application Layer Attacks (OWASP)
Threats such as:
- SQL Injection
- Cross-Site Scripting (XSS)
- Malicious payloads
Target the web application itself — not just the network.
A traditional network firewall alone is often not sufficient to stop these attacks.
The Business Impact
The consequences are not only technical.
They include:
- Slow ERP performance
- eShop instability
- Downtime
- Increased cloud bills
- Risk of data breach
- Loss of customer trust
In many cases, the root cause is malicious traffic that appears “normal” at first glance.
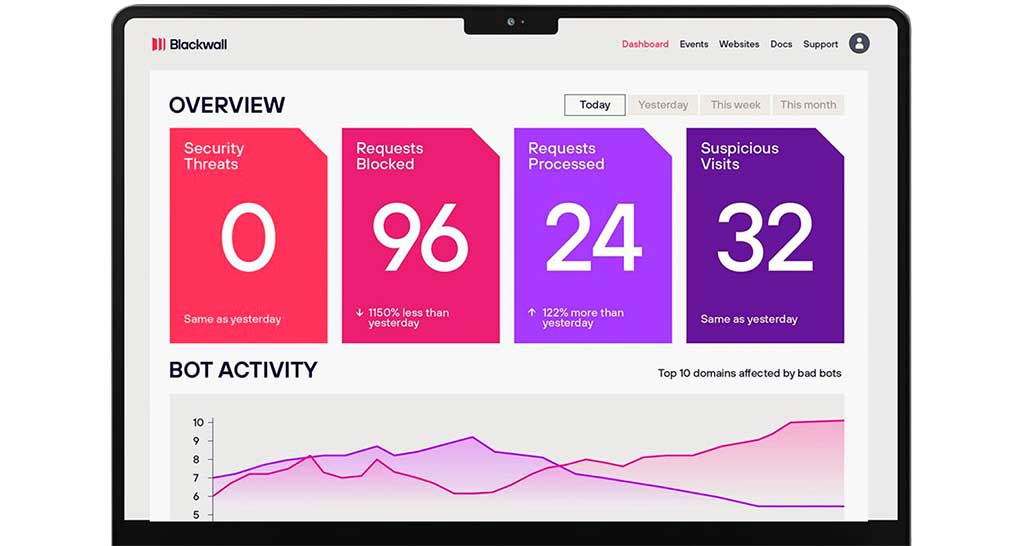
What Is Blackwall?
Blackwall is a Web Application Protection solution that operates as a reverse proxy in front of your website or ERP portal.
It analyzes incoming traffic in real time and:
- Detects and blocks malicious bots
- Prevents brute force login attempts
- Mitigates scraping activity
- Protects against web-layer attacks
- Filters suspicious requests before they reach your server
- Reduces infrastructure load
Blackwall does not replace your firewall or endpoint protection.
It acts as an additional security layer specifically designed for internet-exposed web applications.
When Does It Make Sense?
Web Application Protection is especially important if:
- Your ERP is hosted in the cloud
- You operate a B2B eShop
- You provide public login portals
- You observe unusual traffic spikes
- You want greater visibility and control over incoming traffic
How Protogramma Implements Blackwall
With over 30 years of experience in ERP systems, cloud infrastructure, and business software, Protogramma approaches cybersecurity as part of a broader IT strategy.
We:
- Assess your web exposure risks
- Design the appropriate protection architecture
- Deploy Blackwall in Cloud or On-Prem environments
- Integrate security into your ERP and business operations strategy
Security is not an add-on.
It is a foundation for business continuity.
Want to evaluate whether your ERP or eShop is adequately protected?
Request a consultation
or
Schedule a short discovery call with our team.